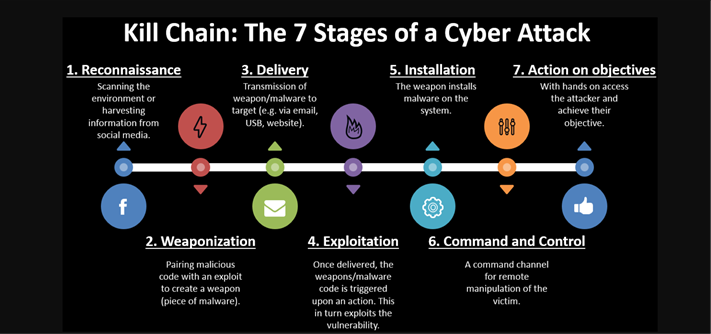
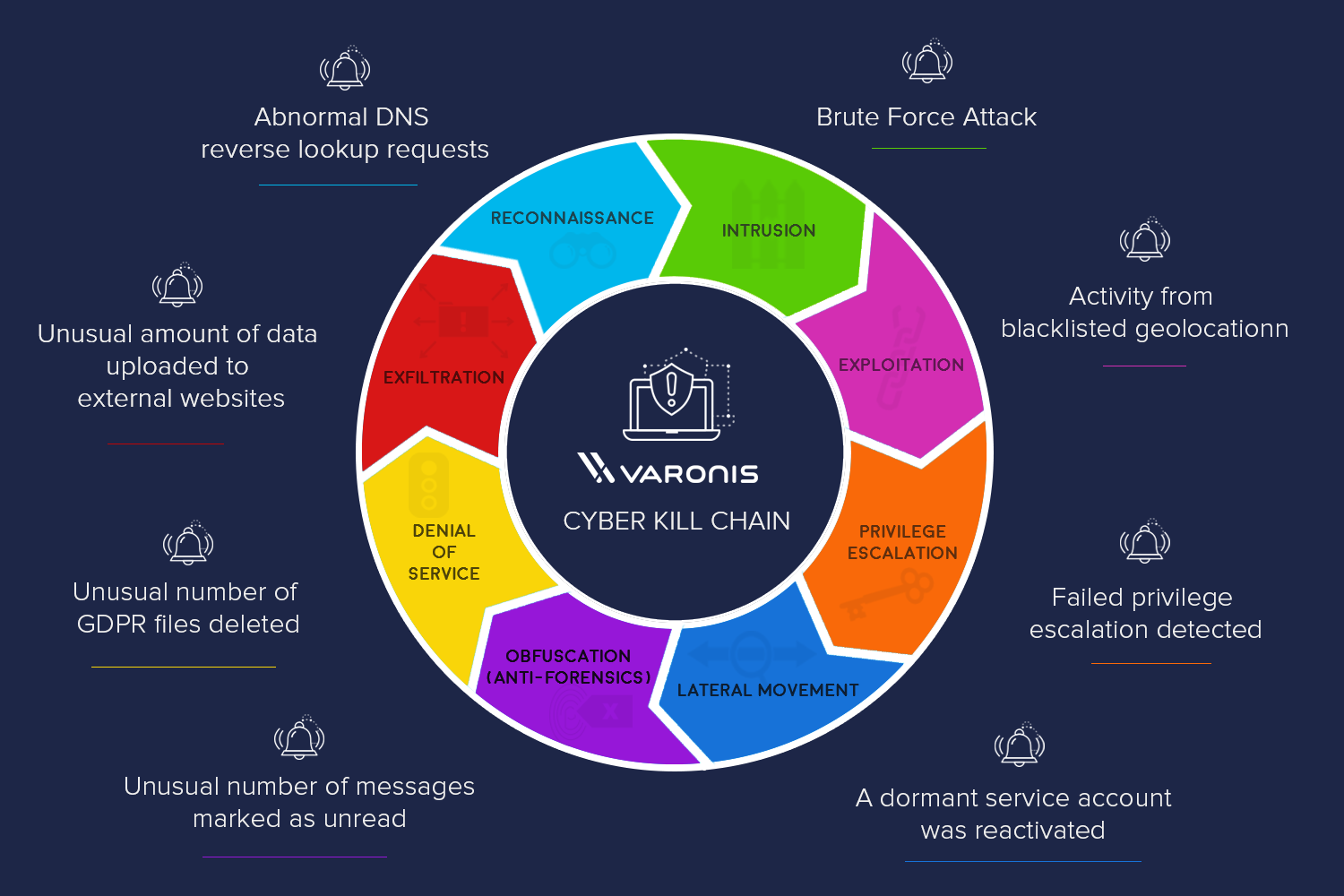
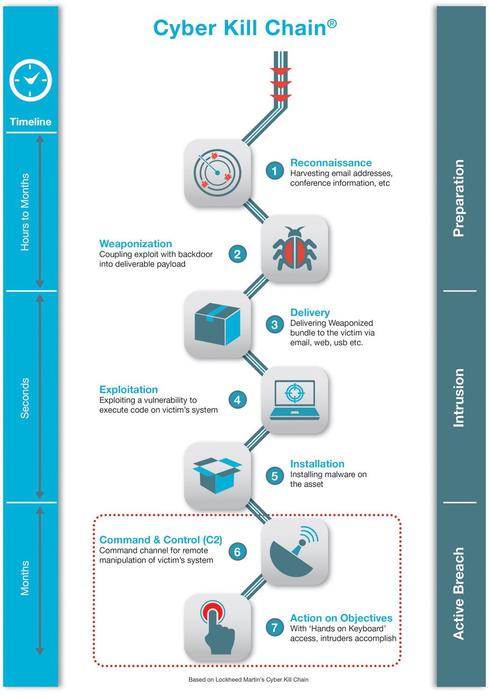
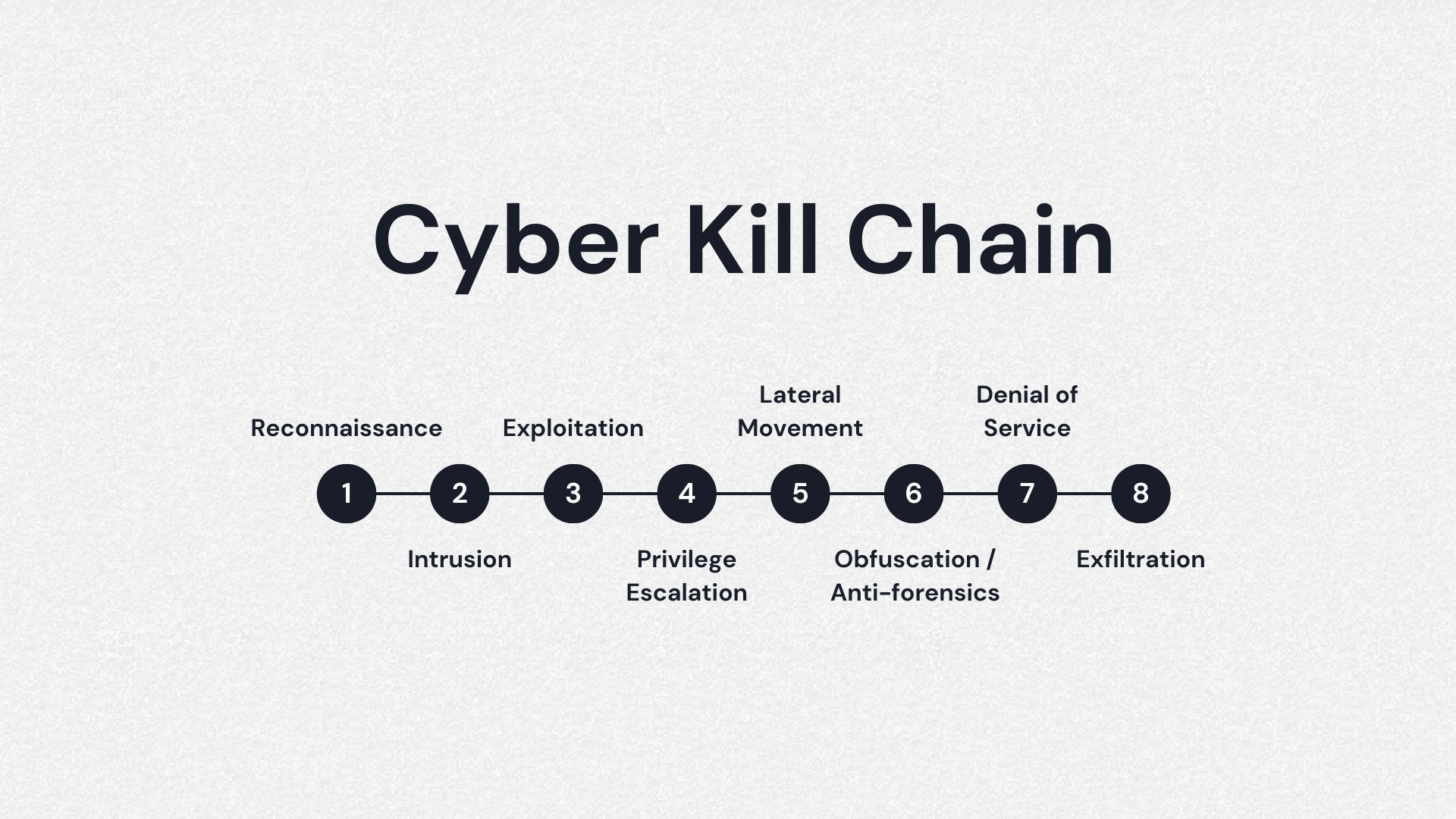
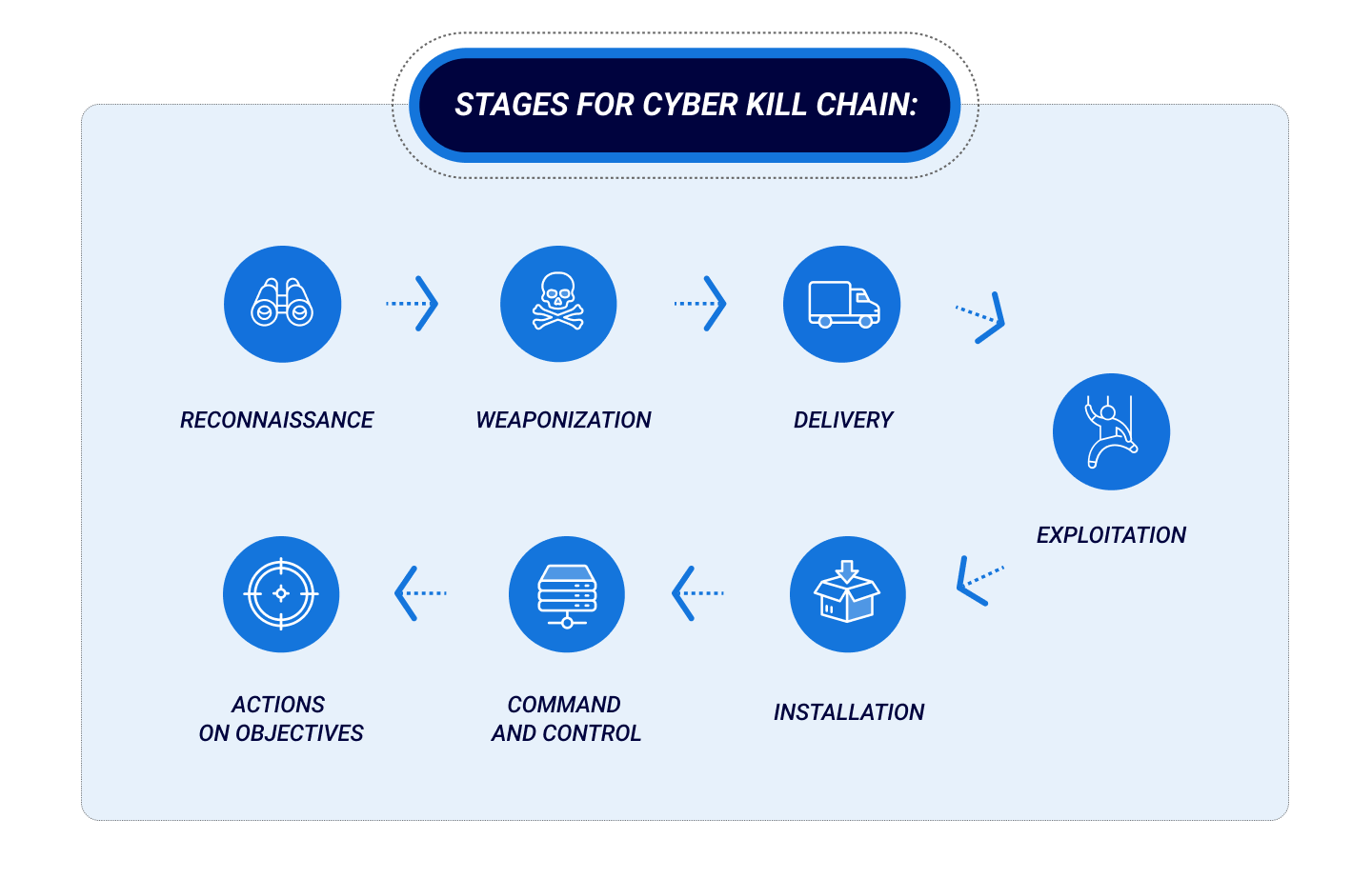
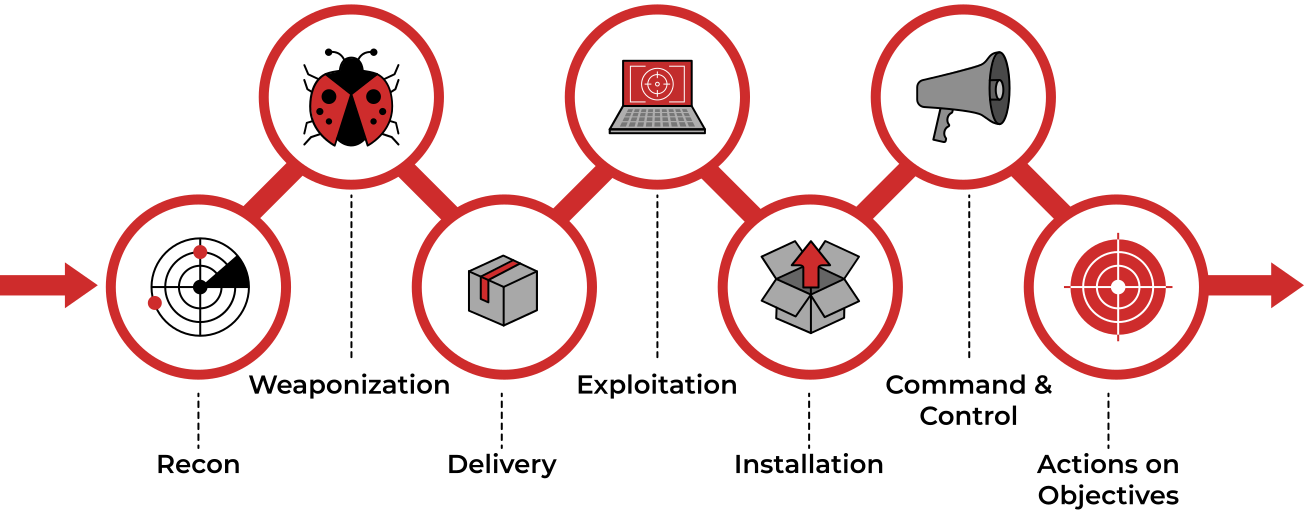
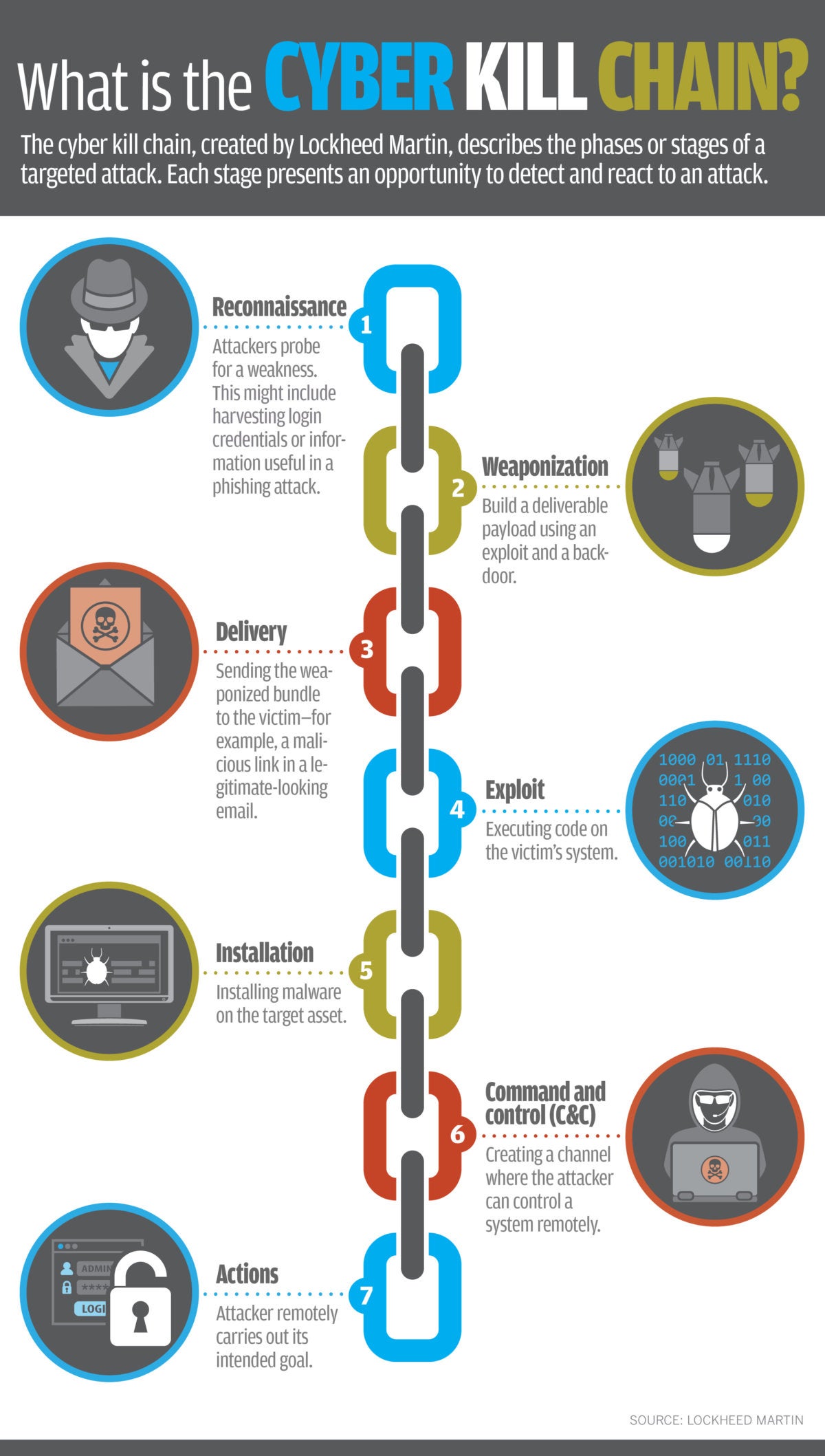
EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber

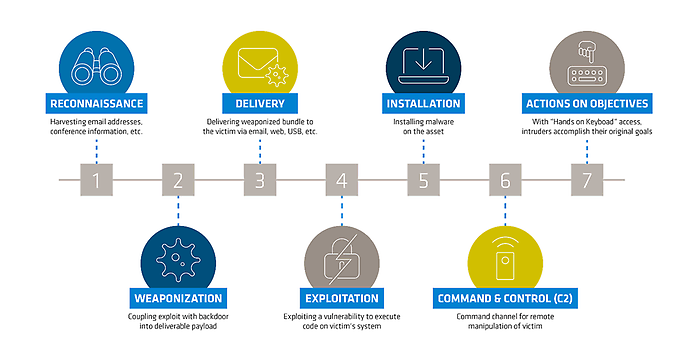
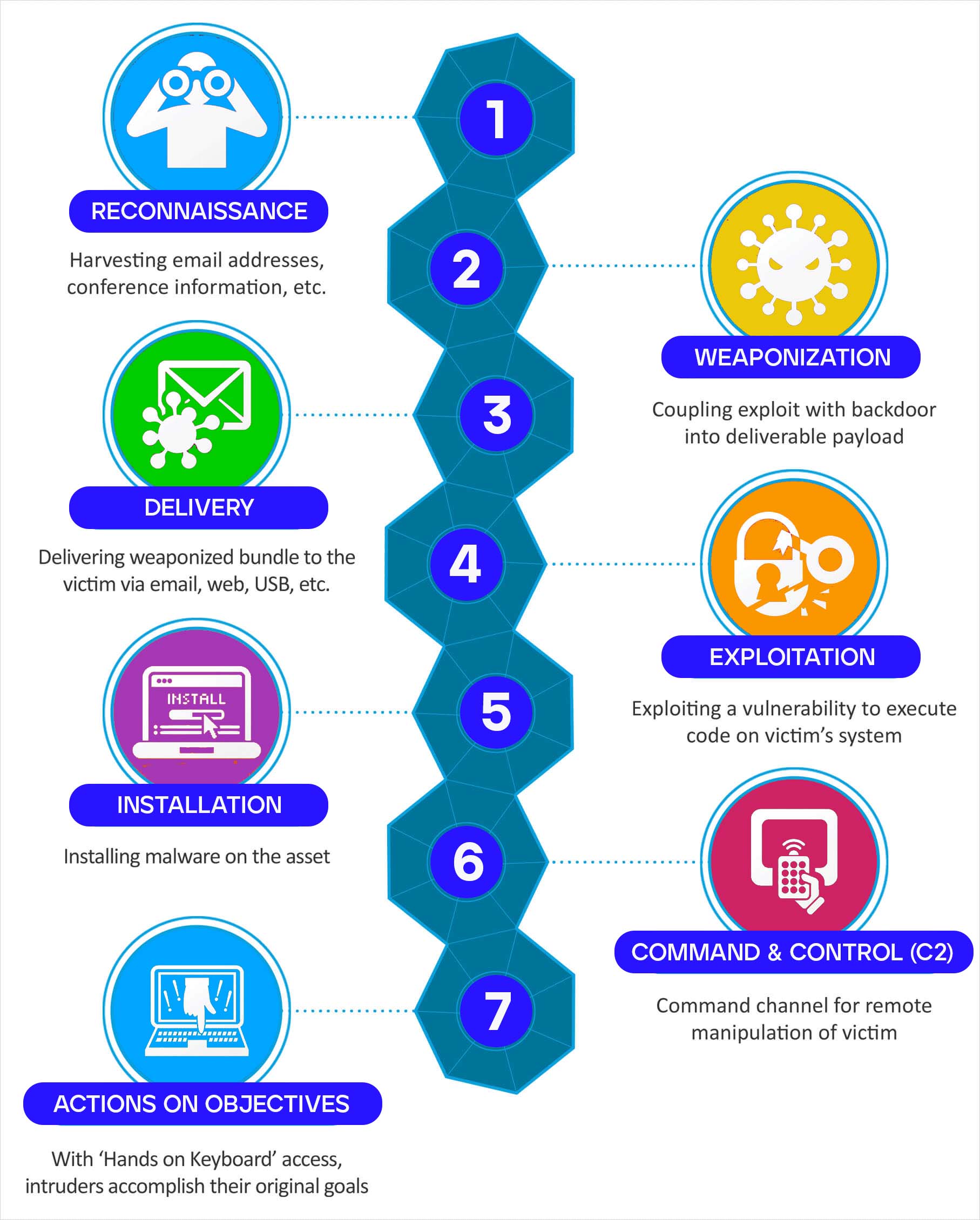
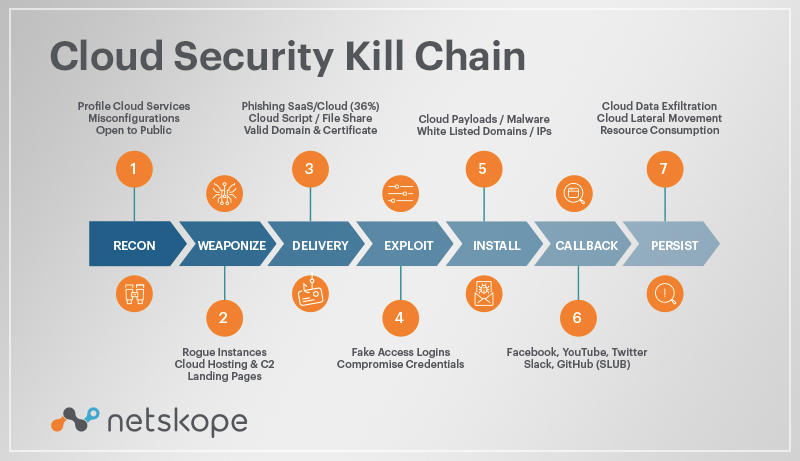
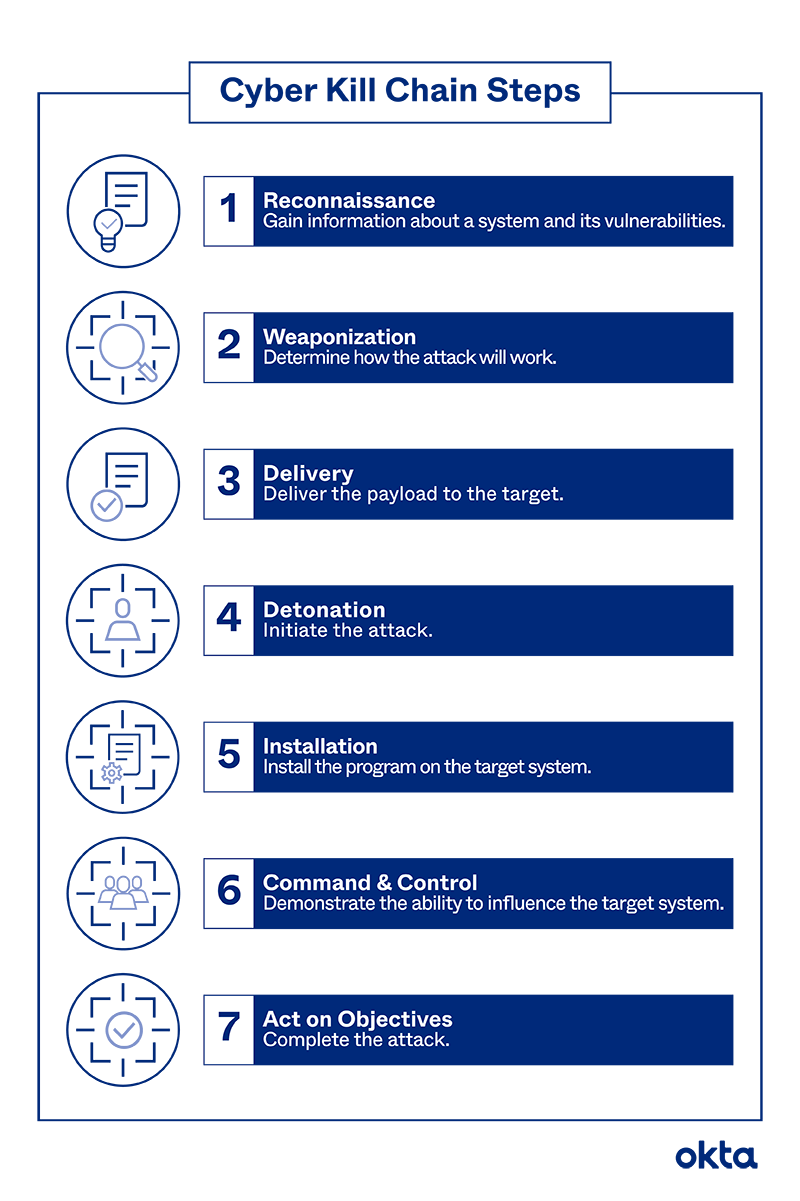
DOD's Utilization of a Cyber Kill Chain Framework to Quantify Cyber Security Investments: Part 3 of the Key Cyber Defense Strategies Series - Government Technology Insider